Firewalls for Small Businesses

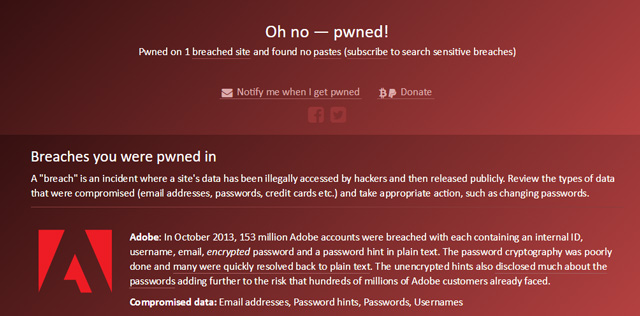
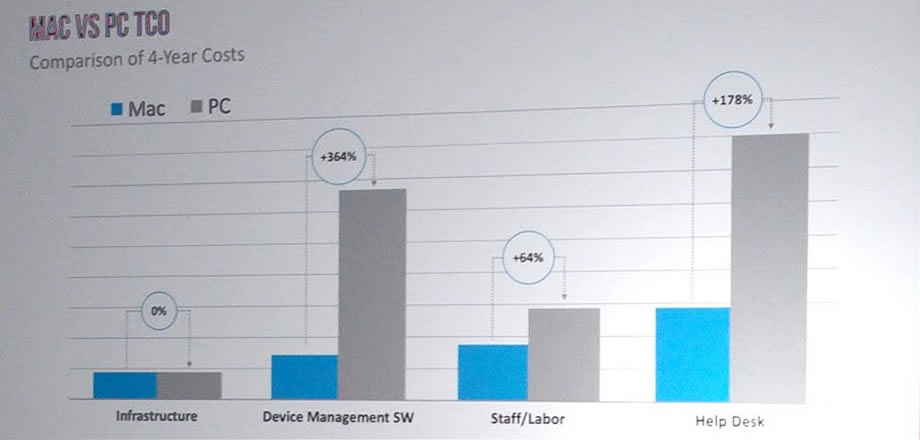
Your business’s firewall is the layer of protection that keeps it safe from outside threats. A quality firewall blocks undesirable incoming traffic while still allowing your business to communicate externally. Does your small business really need a firewall? It’s critical to your overall security and helps keep your business running smoothly. 1. Avoid downtime with a quality firewall. Security threats are growing with every passing year, and many of them can bring your business’s productivity crashing to the ground. For a long time, users believed that Apple products were immune to the bulk of viruses. While it’s true that the same… Read moreFirewalls for Small Businesses
 repair
repair at-home
at-home business
business about us
about us shop
shop off-site-backup
off-site-backup Get Apple Support
Get Apple Support